INFORMATION SECURITY MEASURES UNDER PRESSURE OF REVISION

Takakura Hiroki
What on earth is happening? Is Japan taking information security measures seriously?” This year, one after another of the networks of public organizations and corporations, including major heavy industries, have been at the receiving end of cyber attacks, resulting in disclosure of important information in some instances. The damage is gradually becoming clear as the investigations move forward, but in most cases, we cannot expect to understand the full particulars. In many of the attacks, the attackers penetrated protected computers that were only accessible to a limited number of people at the companies to steal information. A great variety of information was targeted including personal information, military technologies, nuclear power technologies, chemical technologies, and information about affairs of the state.
In this article, we explain why these situations occur and why we cannot prevent attacks, and we also discuss new measures to counter these kinds of attacks.
Countermeasures are delayed
In many of the examples, the cause was clearly attributable to improper operational management, such as neglecting software vulnerability, or connecting unsecured computers directly to the Internet in violation of the rules. There are also examples where the presence of vulnerabilities had been noted, but countermeasures were delayed.
The primary reason for delays, or inappropriate information security measures, is the difficulty of estimating cost-benefit performance. Taking countermeasures incurs expenditure. If we assume a situation where no countermeasures are taken, it is difficult to estimate to what extent the probability of an incident increases, what type of damage would arise in case of an incident, and, how much the damage would cost. If we consider the current situation where software vulnerabilities are reported on a monthly basis, it is inevitable that management wants to curb expenditure by implementing a batch of multiple countermeasures every few months.
The potential for measures taken to counter vulnerabilities in one software product to have an impact on the functions of other software is another reason for not taking any countermeasures until it has been confirmed that no malfunction will occur. The management is also unwilling to take any countermeasures before it is confirmed that their introduction never causes malfunction, because measures taken to counter vulnerabilities in one software product may have an impact on the functions of other software.
Computer software, including operating systems (OS), is made up of detailed vast numbers of modules, i.e., libraries, each of which correlate in complicated ways. For example, the addition function is not only used in spreadsheet applications, but also in word processing applications, mail applications, and every other application under the sun.
For each application to have the same functions is redundant. The OS implements these functions as a library, with each application referring to the library. If we were to draw a comparison with automobiles, it is similar in the sense that they share many parts even though the models vary. If a defect is found in a particular function, only the library where it is contained is replaced with the latest version. Even if the application is not replaced Without replacing the application, it is always possible to use the newest function. It is the same thinking as replacing only the parts that do not work well in automobiles.
What if you have to replace some of the functions of automotive parts in order to deal with defects that have been identified? It is not only a matter of replacing the parts, but you also have to inspect all the models equipped with the function to see if the change will have any negative impact on the overall operation of the automobile.
In case of replacing a library to counter vulnerabilities, the functions inside the library may change. You must thoroughly verify whether or not there is any malfunction in the applications that refer to this function. For example, if it is a question of an accounting application, you have to confirm that there are absolutely no errors in the addition function even if the library is replaced. Generally, it takes several weeks to several months to carry out verification once the library has been replaced.
Unlike automobile recalls, the frequency of OS security updates is extremely high, from every few days to monthly. The investigation of the presence of malfunctions is still ongoing when the next update is provided. Accounting applications etc. where malfunctions are absolutely not permitted are unable to synchronize with frequent OS security updates, and as a result, security updates are postponed and the computer remains in use.
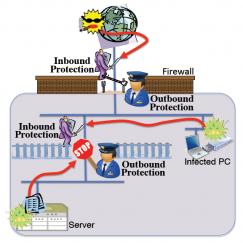
Effective measures to mitigate this risk in the past included lack of access to such computers from outside the company; or the computers were connected to networks that only a limited number of employees could access; or they were standalone computers that were not connected to any internal networks. At the boundaries between the internal network and the Internet, firewalls, intrusion detection systems (IDS) and anti-virus prevent intrusions (possibly even invasions). PCs and USB sticks (external media) brought from the outside are inspected by quarantine systems to prevent malware from entering. Company PCs are loaded with security software that safeguard against internal malware infections. We refer to these countermeasures as inbound protection, which basically uses multistage defenses to protect against intrusion from outside. However, in the current cyber attacks the protection was easily breached.
Breaching inbound protection
In the same way that vaccines for pathogens are created in the field of pharmaceuticals, the anti-virus vendor must acquire samples of malware in order for the anti-virus to prevent malware infection. The vendor analyzes the sample to locate a characteristic series of instructions located inside its machine code. This will serve as the foundation for the detection pattern. The detection pattern is flexible to the degree that it can detect similar malware, but it is not possible to create a universal pattern that covers all malware.
Similarly to the way that a pathogen develops resistance to vaccines by causing its genetic structure to change, the malware causes changes in the series of instructions that attack vulnerabilities to produce variants that the detection pattern is unable to cover. It is also able to encrypt this series and to camouflage it as mere character strings, and not an instruction set. By changing the encryption method, it is able to convert the same series to a different character string, making it impossible for the detection pattern to detect the virus.
Since anti-virus purchases are not screened, the attacker can easily obtain the anti-virus that the targeted organization uses. If the anti-virus is examined, it is possible a quite easy task to verify that a malware created by using the method described above is undetectable. Unlike pathogens, which change according to natural selection, people say that several variants are created every second around the world through artificial manipulation.
Basically, the IDS that are used for inbound protection also use detection patterns. Consequently, in a targeted attack, it is possible to evade all detection and to penetrate internal systems.
Ninja malware
Even if a PC has been infected with malware, people probably think that information cannot be removed stolen as long as the PC is unable to access the Internet. Unfortunately, in reality, the attacker deliberately bides his time, penetrating internal networks, and removing information pulling information out from internal systems, and even from segregated servers. Just like a ninja.
In the first stage of an attack, there are several entry pathways for the malware. The classic pathway is for the attacker to attach the malware to an email sent to a targeted employee. At this point, the individual chosen as the target is not an employee with direct access to the important information being targeted, but a general employee wide-open to a social engineering attack. For example, the attacker sends a CV file disguised as a job application to an employee in the human resources department. The CV file contains malware that cannot be detected by the anti-virus due to the techniques mentioned above. When the employee opens the file, the CV is displayed correctly, but at the same time, the malware infects the employee’s PC.
In addition to emails, attackers also send external media such as USB sticks or DVD media through the postal mail. Other methods include sending an email with a link to a website that downloads the malware when the link is clicked that seems to be ordinary contents, but silently instigates a web browser to download the malware by attacking browser’s vulnerability. Depending on the situation, the attack may span several corporations by first hijacking the website of a client of the corporation targeted for the attack, and planting the malware on the site.
Even if the PC is successfully infected with the malware in the first stage of the attack, the attacker does not immediately try to steal important information. Initially, most malware infection involves a downloader for bringing in other malware from outside the company. They include, for example, a keylogger that lies in wait for keyboard input of IDs and passwords on external websites, or spyware that looks for document files and emails on the PC or the server. Once the downloader has obtained these malicious programs, and installed them on the infected PC that it is now completely under its attacker’s control, the surveillance starts. Now, any information obtained can easily be carried out of the company by accessing websites, or sending emails.
The aim of inbound protection is to prevent external attacks on the company. It does not assume an internal PC turning traitor and actively accessing the outside. Moreover, bringing in malicious programs or taking out information may also be done in the form of uniquely encrypted communication. Consequently, none of the inbound protection systems are able to detect investigate the content of these communications.
Based on information obtained by means of surveillance, the attacker determines the next target for the attack. The choice is often a person who constantly exchanges emails with the user of the hijacked PC. Referring to document files obtained during surveillance, the file where the malware is planted is given a name that the attack target will not find suspicious, and is then attached to an email the malware is planted to the file and then the file is attached to an email, so that the attack target will not find any suspiciousness of its name. In addition, the hijacked PC is constantly monitored, and by impersonating the user of the PC, the emails are even timed exchanged as if engaged in a conversation. By repeating surveillance and attacks in this way, the attacker gradually closes in on the person with access to the important target information.
There is a good likelihood that any PC able to access important information is also prohibited from accessing the outside. It is traditional protection that any PC able to access important information is prohibited from accessing the outside. In that case, previously hijacked PCs function as relay stations for taking out important information. In addition, servers where confidential information is stored may be standalone and segregated from internal networks. However, servers are installed deployed in order for the confidential information to be used, so it is essential to have some way of entering or removing retrieving, and transporting confidential information. Generally, USB sticks and other external media are used. If the use of such media is understood through surveillance, the PC that functions as a relay station is used as an intermediary for bringing in malware that spreads the infection. If the use of such media is ascertained through surveillance, the PC that functions as a relay station is ordered to use the media as an intermediary that brings malware into the server and carries its confidential information out.
Standalone servers are easily infected by malware because vulnerabilities are often neglected, as it is troublesome to update the OS, or out of a sense of security brought on by the segregation from the internal network. Every time external media are connected, the malware that has infected the server attempts to use the media as an intermediary for removing stealing the confidential information it has found.
It is difficult to carry out the activities described above in a short time. If the value of the targeted information is high, attackers may even spend years on it. During that time, it is possible that the anti-virus will detect the planted malware. In order to securely continue surveillance and attacks over a long period of time, a single PC is infected with different malware to multiply the means of communication with the outside. Depending on the update situation for anti-virus detection patterns, the malware is regularly replaced at intervals as frequent as every few minutes. This is how the activity continues.
When a PC that has acted as a relay station is no longer needed, any traces or communication records that can be used to detect investigate the activity are deleted, and counterfeit records are added. Due to such evasive maneuvers, it is difficult to analyze the incident after detection.
Limitations of National Laws and Treaties
On June 17, 2011, legislation was adopted to revise sections of the penal code and other laws to deal with the increasing sophistication of information processing. In the past, charges could not be laid unless there were damages, such as destruction of the personal property of other people, or obstruction of business, but under the revised law, the act of creating, providing, obtaining, or storing malware under certain conditions, such as lack of legitimate reason, is unlawful. With this revision, the environment for ratifying treaties on cyber crime has been made ready, and it is now possible to punish those involved even if the cyber crime spans several countries. This is expected to have a deterrent effect on cyber crime by perpetrators in Japan.
However, as already mentioned, the modus operandi for cyber crime are rapidly growing in sophistication, and even identifying what information has been stolen is increasingly difficult, let alone the tracing an invasion. The stolen information is successively transmitted to servers outside the country, and in many cases, the attackers have also hijacked the computers at the destination. Information linked to identifying the attackers is deleted, or falsified. It is no easy matter to confirm the identity of the attackers, or to request punishment based on treaties involving overseas countries where these computers are installed. In addition, cyber attacks where there is suspicion of state involvement are also on the rise, which is difficult to handle using current national laws and treaties.
New information security countermeasures
To begin with, we must review the conventional method of inbound protection. To use a simile, inbound protection is something akin to enclosing the perimeter of a farm with fencing, and only standing guard at the gate. In the past, there were no occurrences of attacks by climbing over the fence, so it was fine if you only paid attention to attacks that tried to pass through the gate.
Recent attacks have involved climbing the fence, or passing through the gate under the guise of harmlessness, and then running amok inside the fence. Assuming an attack that slips through inbound protection, it is now necessary to have information security measures that protect the network inside the organization in multiple ways, similar to a castle surrounded by moats and several ramparts. In order to prevent activity inside the company, it is also important to guard the internal networks. As mentioned above, attackers gradually penetrate to the core of internal networks to bring out important information. We need frameworks that pick up on the invasion before the attacker arrives at the important information.
To start with, there is a need to change the network structure in order to reduce the quantity of communication by the target for surveillance. Presently, with the exception of segregated networks and standalone servers, there is free communication between PCs on the average commonly used network. We will change this network structure to a network with access restrictions for each department. As a result, it will be easy to prevent direct attacks from infected PCs, or communication between PCs that act as relay stations.
In the past, such a network would have required physical network cables at each department. Every time a desk was moved, the cables had to be refitted rewired, making for poor feasibility. However, by using VLAN (Virtual LAN) technology, it is now possible for several LAN to share a single cable. It is possible to respond to changes in desk arrangements by simply changing the configuration of network switches. Concerning wireless LAN, it is possible to set up that single access point is set up several ESSID (Extended Service Set Identifier), and for each ESSID, there is an increase in access points that can be allocated to the VLAN that each ESSID is assigned to different VLAN.. If ESSID are set up for each department, it is easy to implement these types of access controls. The cost of network maintenance will increase, but this approach is essential for the future.
Next, IDS and firewalls are installed deployed at every important point of communication between VLAN. Malware communications may be encrypted, making it impossible to detect malicious communications by these devices. However, there is a high probability of a firewall blocking attempts at malware communication at a stage when surveillance is still insufficient. However, there is a high probability that a firewall betweeen VLAN blocks attempts caused by malware communication at an early stage when surveillance is still insufficient. Consequently, the log of what the firewall blocked is recorded, confirming whether or not the IDS has detected a scan attack, and making it possible to detect malware infection in the early stages. Consequently, the logs of what the firewall blocked is recorded and of whether or not the IDS has detected a scan attack should be confirmed to detect malware infection in the early stages.
In addition, systems that are on the lookout for access to, or removal of copy from, restricted files have started to emerge been announced for servers that hold important information. By combining these systems with outbound protection, frameworks that prevent the removal stealing of important files have also become conceivable. In cases where the quantity of logs and warnings is excessive, making manual confirmation difficult, there is a need for systems that focus on and analyze only abnormal communications that do not usually occur. These systems are in the development stages, but it is conceivable that many security vendors will be able to provide them in the future.
Growing disparity
Since the earthquake disaster, there has been a rapid increase in cyber attacks targeting Japanese corporations and public offices. It is not only a matter of targeting defense technologies, but also information about the sophisticated technologies that are the pride of Japan, as well as information about the affairs of state. If this information is continues to be leaked, Japan will lose its international competitive strength. Specifically Currently, the issues around information security in Japan involve the Ministry of Defense, the Ministry of Foreign Affairs, the Ministry of Economy, Trade and Industry, the Ministry of Internal Affairs and Communications, the National Police Agency and many other ministries and government offices. As a result of insufficient collaboration between these organizations, committees and investigative commissions are organized at each ministry and government office, resulting in a situation where the same discussions are repeated. The issues differ for each ministry and government office, and while we do not believe that the issues could be resolved if there were a single organization, such as a Ministry of Information Security, we do believe that for the state, it is a matter of some urgency to construct an approach for taking prompt and efficient countermeasures.
When we consider the scale of expenditure necessary for the recovery from the earthquake disaster, it is difficult to bring up any increase in the budget for information security, but we will presume to mention it. According to data from the Information Security Policy Council at the National Information Security Center, the budget for research and development of information security in Japan was 4.86 billion yen in fiscal 2010, which is a decrease of 47% over a period of five years. Meanwhile, the budget for fiscal 2010 in the United States was 36.6 billion yen, which is an increase of 91% over a period of five years. Other major countries show similar tendency to United States. It may be that simply comparing amounts of money is of no significance, but the impact of this disparity is already starting to show.
In the United States, industry, government and academia as a whole collect information on cyber attacks, and continue to analyze and develop systems for countermeasures. As for cyber attacks occurring at major heavy industry, the United States has been aware of the seriousness of the issue since 2008, and has steadily worked on getting ready for it. The results are starting to show with the United States announcing a succession of new systems for responding to these types of cyber attacks in this year when they have become an international threat.
There have been a succession of cyber attacks targeting only Japan, and in one train of thought it would be good to provide this information to research institutions worldwide, sharing the necessary expenditure, and getting them to think about provide us with countermeasures. However, if the cyber attacks are sophisticated, purchasing response defense systems alone will have no effect, as sophisticated knowledge is necessary to handle these systems. Moreover, in case of an extremely sophisticated attack, the collected information is obviously only shared with domestic research institutes, and not with other countries, in order to protect the national interests of Japan the country.
Perhaps it is inappropriate to say this, but at a time when the attackers are circling Japan like looters at the scene of a fire, we must gradually change our attitudes to whether countermeasures that in large part depend on other countries are acceptable, and whether this is sufficient to protect the intellectual property of Japan from cyber attacks.


